Cyber Resilience Built for Post-Breach Reality
Cyber Resilience Built for Post-Breach Reality
The EchoLeaf SafeRoom™ is the only patented, physically air-gapped, immutable, and ransomware-proof cyber vault, purpose-built to shield essential data from attack, and enable rapid recovery when it matters most...the last mile of defense™!
The EchoLeaf SafeRoom™ is the only patented, physically air-gapped, immutable, and ransomware-proof cyber vault, purpose-built to shield essential data from attack, and enable rapid recovery when it matters most...the last mile of defense™!

Delivered Through Trusted Technology Partners
The Reality of Modern Recovery
Post-Breach Recovery Requires the EchoLeaf SafeRoom™
Are you ready when a breach happens?


Echo Your Data™
Create, verify, and preserve an immutable, known-clean recovery copy protected from ransomware to enable post-breach operational resilience.


The Last Mile of Defense™
A patented cyber recovery vault that physically isolates recovery data, serving as the final safeguard for restoring critical systems after ransomware or destructive attacks.


Sustainable by Design
EchoLeaf’s managed tape-based architecture delivers long-term resilience while using far less energy than disk or cloud storage.
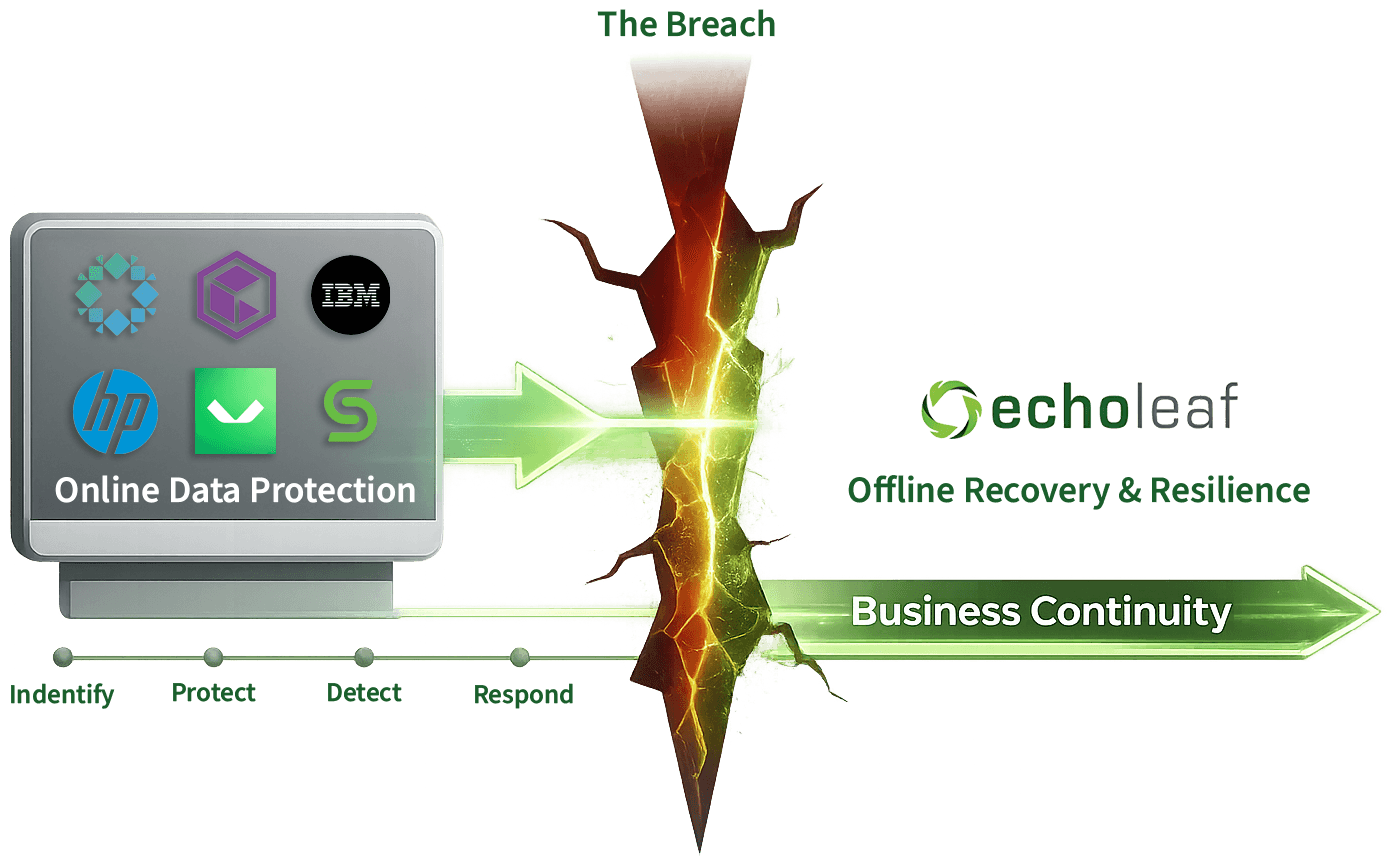
Built to Complement, Not Replace, Your Backup Platforms
Built to Complement, Not Replace, Your Backup Platforms
EchoLeaf integrates seamlessly with your connected online data protection and backup platforms. It does not replace your tools or workflows. Instead, it adds a final, physically isolated resilience layer that protects a trusted recovery copy outside the reach of malware or automation…the last mile of defense™!
EchoLeaf integrates seamlessly with your connected online data protection and backup platforms. It does not replace your tools or workflows. Instead, it adds a final, physically isolated resilience layer that protects a trusted recovery copy outside the reach of malware or automation…the last mile of defense™!
The EchoLeaf SafeRoom™ Advantage
Four Pillars of Resilience
Purpose-built capabilities that protect clean recovery data beyond the reach of attackers and automation.
The Platform
See the SafeRoom™ in Action
A unified dashboard for archive management, security, performance monitoring, and disaster recovery. Operational visibility across every pillar, in one place.
Real-time 24/7 monitoring across all SafeRoom™ systems
Instant alerts with severity classification for critical events
Full operational transparency into jobs, security, and recovery readiness

The Platform
See the SafeRoom™ in Action
A unified dashboard for archive management, security, performance monitoring, and disaster recovery. Operational visibility across every pillar, in one place.
Real-time 24/7 monitoring across all SafeRoom™ systems
Instant alerts with severity classification for critical events
Full operational transparency into jobs, security, and recovery readiness

The Platform
See the SafeRoom™ in Action
A unified dashboard for archive management, security, performance monitoring, and disaster recovery. Operational visibility across every pillar, in one place.
Real-time 24/7 monitoring across all SafeRoom™ systems
Instant alerts with severity classification for critical events
Full operational transparency into jobs, security, and recovery readiness

U.S. Patent Protected
The Foundation for Reliable Recovery after Compromise
The Foundation for Reliable Recovery after Compromise
Protected by a U.S. patent for aggregated control and virtualization of removable digital storage media (RDSM), enabling EchoLeaf to virtualize tapes and other removable media into a unified archive and support full system reconstruction after a major breach.
Protected by a U.S. patent for aggregated control and virtualization of removable digital storage media (RDSM), enabling EchoLeaf to virtualize tapes and other removable media into a unified archive and support full system reconstruction after a major breach.

Insights From the Front Line of Data Resilience
Perspectives on post-breach recovery, cyber resilience, and the architectural decisions that determine whether organizations can recover with confidence.

Post-Breach Cyber Resilience
Built for the moment recovery matters most
See how physically air-gapped recovery changes what’s possible after a breach.

Post-Breach Cyber Resilience
Built for the moment recovery matters most
See how physically air-gapped recovery changes what’s possible after a breach.

Post-Breach Cyber Resilience
Built for the moment recovery matters most
See how physically air-gapped recovery changes what’s possible after a breach.